Key Takeaways
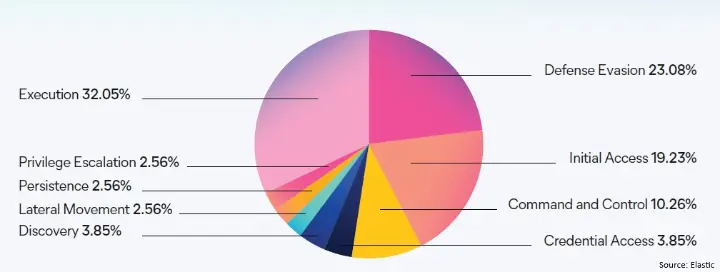
- On Windows, Execution became the top malicious tactic at 32.0%, roughly doubling its prior share and overtaking Defense Evasion.
- Over 60% of cloud security events cluster around Initial Access, Persistence, and Credential Access, showing how concentrated cloud attacks are around identity.
- More than 1 in 8 malware samples were designed to steal browser data, while Generic threats rose 15.5%, likely helped by AI lowering the barrier to create simple malicious tools.
One thing is becoming hard to ignore from the 2025 Elastic Global Threat Report.
Attackers are starting to operate a lot like modern digital businesses.
They use speed, automation, trusted platforms, and repeatable playbooks. They move through cloud accounts, browsers, and developer environments because that is where real business now happens.
That has a direct implication for AI and automation leaders.
The real lesson is not just “add more security.” It is to design automation, developer workflows, and identity controls with the assumption that compromise can happen in minutes. If your detection strategy still leans heavily on signatures, you are fighting yesterday’s battle. Speed now beats stealth, and context beats static rules.
In practice, that means:
💎 Adopting automation with human-in-the-loop oversight
💎 Strengthening browser defenses
💎 Elevating identity validation
💎 Prioritizing memory protection
💎 Securing the development and supply chain ecosystem
To us, that is the strategic shift.
Security can no longer sit on the sidelines while AI, cloud, and automation reshape the core of the business. It has to be embedded in how work gets done, how identities are verified, and how code is built and shipped.
Are your teams still leading with endpoint defense, or are you already rethinking security around the browser, identity, and developer workflows where today’s attacks actually unfold?
#CyberSecurity #CloudSecurity #AISecurity #Automation #IdentitySecurity #DevSecOps
What are the biggest cybersecurity threats in 2025 for cloud, AI, and automation teams?